Google released its built-in optimization feature named Data Saver officially in January 2014. It renamed the feature to “Lite Mode” and kept it for Android devices only since March 2019. The feature is meant to reduce the data usage on your mobile device by loading web pages which are compressed by the Google servers.
As the Data Saver feature is deprecated, let's talk about the Lite Mode which is Android-only and not available on the desktop version of Chrome.
The Feature
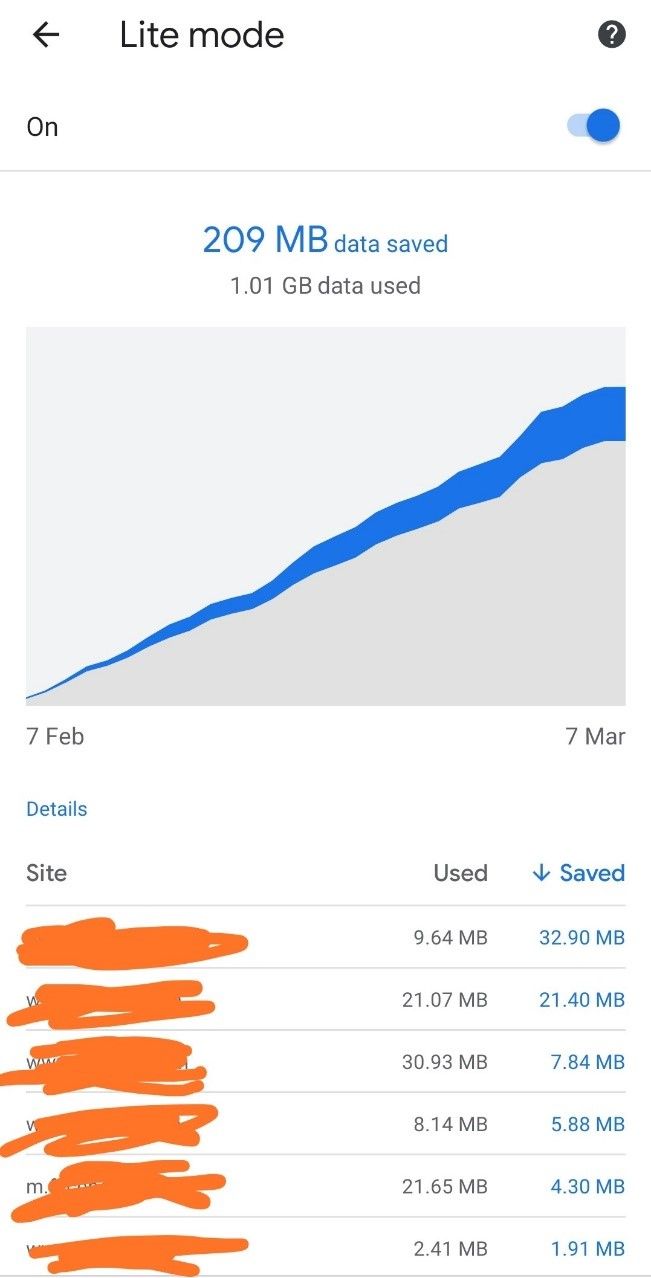
Aiming to reduce the network data usage, Google initially launched it as an extension to Chrome desktop, and later removed it. The feature also gives an option to see how much data was saved using Lite mode. Below is the screenshot of a phone which used 1.01 GB of data in a week and saved 209 MB of data which is around 20% of savings. It also shows what websites were visited and the data saved on browsing.
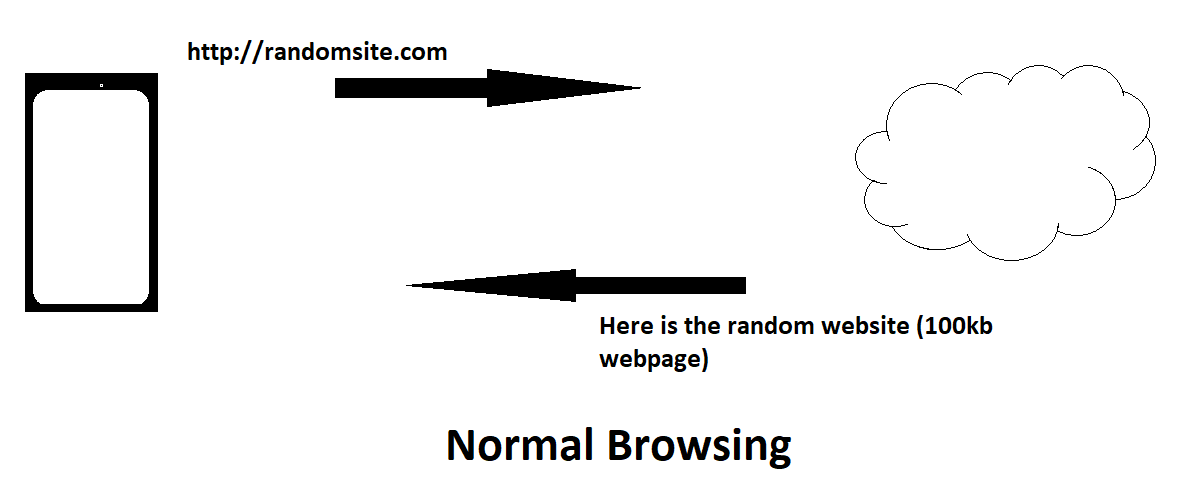
This feature uses the standard Transparent Proxy to see the URL requests, forward the requests to the servers on behalf of the client, download the webpage to its servers, compress it and sends the data back to the user which is of lesser size than the original one. We have tried to differentiate between the regular browsing and Lite Mode browsing with the below diagram.
In times of mobile network, where 4G internet data is highly chargeable, this is an efficient feature that reduces data usage with a significant margin without making a compromise with the quality of information or time taken to load the webpage. However, does it all come at the cost of privacy?
Privacy and Security
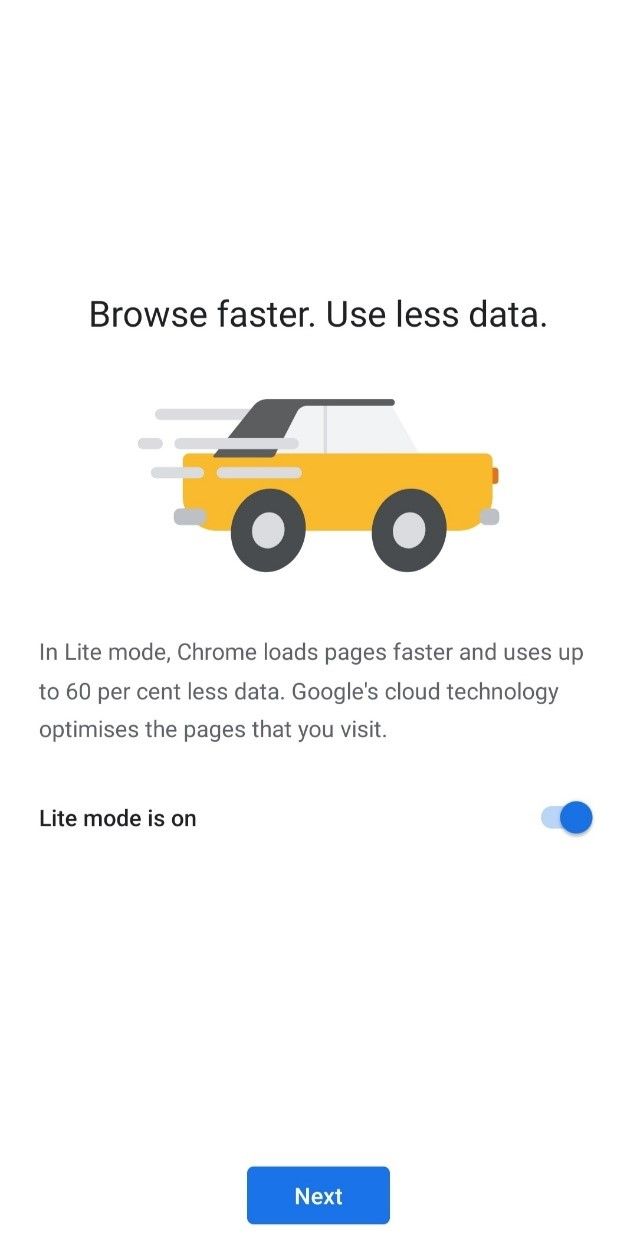
Let's start with the very beginning of Google Chrome set up on your phone.
The second option gives you the option to disable Lite Mode. You're right, it is enabled by default. This is the first step where you can know if there is such a feature in Chrome and understand how it works. A conscious user will go through all the details of the feature and then choose to enable or disable this feature.
The good thing is Google shows you if a website is loaded with "Lite Mode" you'll see the flash icon beside your browser address bar.
The first major privacy challenge is that Google collects the URLs you're using, although passing through its web servers, its servers can also see and download the content you're browsing. According to Google Chrome Whitepaper, Chrome doesn't send the user input information such as cookies or personal data.
https://www.google.com/chrome/privacy/whitepaper.html#datacompression
The second major security challenge arrives with the use of HTTPS websites which are supposed to be TLS encrypted connections with the destination servers. If you're accessing SSL secured websites such as Facebook or Twitter, how does “Lite-Mode” handle that?
The curse of SSL Proxy
The transparent proxy servers are the epitome of end-user helplessness, as there is no way you can control if you want to be intercepted by the Network owners or not. The intercepting devices are sitting on the pathway between your device and the internet/webserver. When using an SSL session, the only thing visible is the website domain of the webserver you're accessing. For example, you may be browsing groups, uploading pics, and status, etc on your Facebook, but a network sniffer can only see that you have an encrypted channel with facebook.com. So, in order for Lite Mode to work, it needs to decrypt that channel. How does it do that? Like every other SSL Proxy:
An SSL proxy catches every packet from the beginning and relays the information with the webserver, and ultimately creates the same symmetric-key which is used by both parties to decrypt/encrypt the web traffic. This is achieved by the Chrome Proxy servers to pose as the actual web servers and generating a pseudo-certificate with the domain of the intended web server. This is well explained by network giant Juniper documentation - https://www.juniper.net/documentation/en_US/junos/topics/topic-map/security-ssl-proxy.html#ssl-proxy-graphic
So, an SSL proxy server sees all the communication between the client and web server which is supposed to be encrypted and not to be seen by a third party. An SSL Proxy server is generally used by restricted campuses, or where the user intentionally configures an explicit proxy to be used in order to achieve anonymity with the webserver.
The HTTPs websites' cached pages are served by Google with its own domain means that you're not visiting the websites intended, but the Google web server which downloaded and page and served to you. This raises the question of conscious of the information you're being served by Google Lite Mode proxy.
Google claims that the information provided through Lite Mode pages are not changed while serving the web pages. However, does the actual website owner agree with this clause? Is it agreed with the webserver that their pages are cached on Google servers for 14 days and are served to the end-users? Do they still hold the ownership and accountability of the data being served by Lite servers?
So far, we have not read or heard the owners of the website providing a clause or agreement related to their web pages being served by Google. In case of a variety of information in such cases, who can behold accountably? Google who is actually sending that information, or the webserver from where the information was originated?
Despite Google's intention and claims, the problem resides in the default turned-on feature and their ability to peek through all the data if Lite Mode is enabled.
Please do write us back if you have more information about this topic or would like to correct mistakes. We're always open to suggestions and corrections to keep the best of information to the users.
Write to us at [email protected]

